FBI charges Ukrainian national Mark Sokolovsky for identity theft and his alleged role in operating Raccoon Infostealer malware to infect devices

The US Department of Justice (DOJ) today has charged 26-year-old Ukrainian national Mark Sokolovsky for his alleged role in an international cybercrime operation known as Raccoon Infostealer. The DOJ also charged Sokolovsky “with conspiracy to violate the Computer Fraud and Abuse Act, money laundering, wire fraud, and aggravated identity theft.”
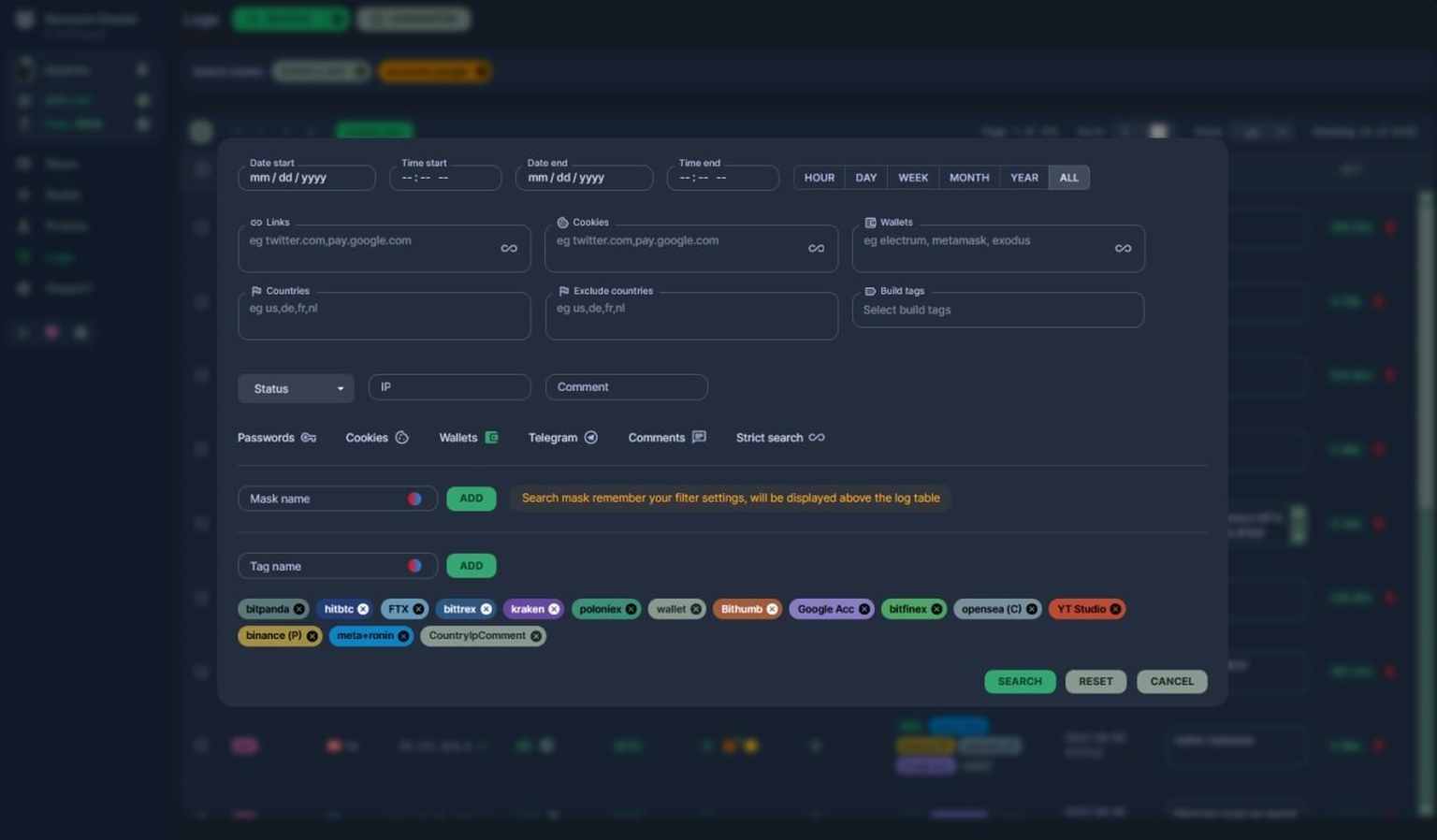
Raccoon Infostealer is a trojan or malware distributed under the MaaS (malware-as-a-service) that infects computers and steals personal information, including email addresses, identification numbers, bank account information, and cryptocurrency information.
Raccoon Infostealer is a very popular malware used by threat actors. Customers can rent Raccoon Infostealer for $75/week or $200/month—using cryptocurrency like Bitcoin—which then allowed them to gain access and deploy Raccoon to obtain a copy of the data stolen from their Victims.
It can be used to steal a wide range of personal information from infected devices, including stored browser credentials and information, credit cards, cryptocurrency wallets, email data, and various other types of sensitive data from numerous applications. Criminal actors can also use the stolen information to commit identity theft, financial fraud, or other crimes.
According to DOJ, Sokolovsky is alleged to be one of the key administrators behind the Raccoon Infostealer, which has infected computers in many countries from 2018 through early 2022.
“[Sokolovsky] has been charged with conspiracy to violate the Computer Fraud and Abuse Act, money laundering, wire fraud, and aggravated identity theft,” DOJ said in a news release this evening.
According to the unsealed indictment, Sokolovsky (also known online as raccoonstealer, Photix, and black21jack77777) was arrested by Dutch authorities in March this year. He’s currently jailed in the Netherlands while waiting to be extradited to the United States.
“This case highlights the importance of the international cooperation that the Department of Justice and our partners use to dismantle modern cyber threats,” said Deputy Attorney General Lisa O. Monaco. “As reflected in the number of potential victims and global breadth of this attack, cyber threats do not respect borders, which makes international cooperation all the more critical. I urge anyone who thinks they could be a victim to follow the FBI’s guidance on how to report your potential exposure.”
Raccoon Infostealer was sold on cybercrime forums such as Exploit[Jin. The conspiracy interacted with its criminal customers, providing them with customer service and information about updates to the Raccoon software and functionalities.
“I applaud the hard work of the agents and prosecutors involved in this case as well as our international partners for their efforts to disrupt the Raccoon Infostealer and gather the evidence necessary for indictment and notification to potential victims,” U.S. Attorney Ashley C. Hoff said. “This type of malware feeds the cybercrime ecosystem, harvesting valuable information and allowing cybercriminals to steal from innocent Americans and citizens around the world. I urge the public to visit the FBI’s Raccoon Infostealer website, find out if their email is within the stolen data, and file a victim complaint through the FBI’s IC3 website.”
Meanwhile, the FBI has also launched a website to let anyone input their email address to determine whether it is contained within the U.S. government’s repository of Raccoon Infostealer stolen data. The website is raccoon.ic3.gov. If the email address is within the data, the FBI will send an email to that address notifying the user.
Potential victims are encouraged to fill out a detailed complaint and share any financial or other harm experienced from their information being stolen at the FBI’s Internet Crime Complaint Center (IC3) at ic3.gov/Home/FileComplaint.
mark-sokolovsky-raccoon-stealer-unsealed-indictment