Google says Apple and Android phones were hacked by Italian spyware

Google announced on Thursday that Apple and Android smartphones in Italy and Kazakhstan were hacked by an Italian company’s hacking tools. According to the report, the tech giant said that Milan-based RCS Lab, whose website claims European law enforcement agencies as clients, developed tools to spy on private messages and contacts of the targeted devices, Reuters reported.
Google’s findings on RCS Lab come less than a year after US officials’ phones were hacked by Israeli NSO Group spyware. At least nine iPhones of US state department officials were hacked using the Israeli startup spyware.
In a statement on its website, Google said that it “has been tracking the activities of commercial spyware vendors for years, and taking steps to protect people.” In 2021, Google also added that its Threat Analysis Group (TAG) discovered seven of the nine zero-day vulnerabilities that fall into developed by commercial providers and sold to and used by government-backed actors categories.
Google said its TAG “is actively tracking more than 30 vendors with varying levels of sophistication and public exposure selling exploits or surveillance capabilities to government-backed actors.”
“Today, alongside Google’s Project Zero, we are detailing capabilities we attribute to RCS Labs, an Italian vendor that uses a combination of tactics, including atypical drive-by downloads as initial infection vectors, to target mobile users on both iOS and Android. We have identified victims located in Italy and Kazakhstan,” Google said in its report.
Google also added that it had taken steps to protect users of its Android operating system and alerted them about the spyware.
Below is the full detail of the hack.
“Campaign Overview
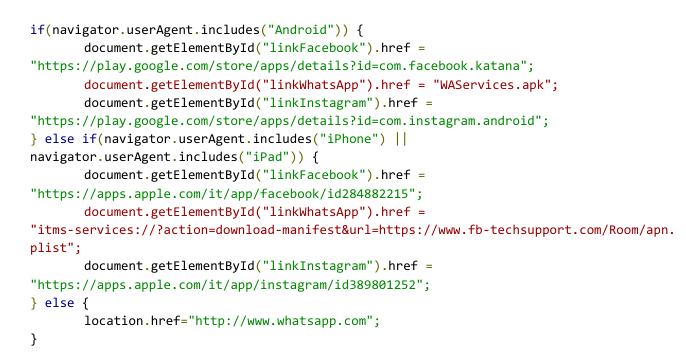
All campaigns TAG observed originated with a unique link sent to the target. Once clicked, the page attempted to get the user to download and install a malicious application on either Android or iOS. In some cases, we believe the actors worked with the target’s ISP to disable the target’s mobile data connectivity. Once disabled, the attacker would send a malicious link via SMS asking the target to install an application to recover their data connectivity. We believe this is the reason why most of the applications masqueraded as mobile carrier applications. When ISP involvement is not possible, applications are masqueraded as messaging applications.
![An example screenshot from one of the attacker controlled sites, www.fb-techsupport[.]com.](https://storage.googleapis.com/gweb-uniblog-publish-prod/images/pasted_image_0_11_cozugbj.max-1000x1000.png)
An example screenshot from one of the attacker-controlled sites, www.fb-techsupport[.]com.
The page, in Italian, asks the user to install one of these applications in order to recover their account. Looking at the code of the page, we can see that only the WhatsApp download links are pointing to attacker controlled content for Android and iOS users.
iOS Drive-By
To distribute the iOS application, attackers simply followed Apple instructions on how to distribute proprietary in-house apps to Apple devices and used the itms-services protocol with the following manifest file and using com.ios.Carrier as the identifier.
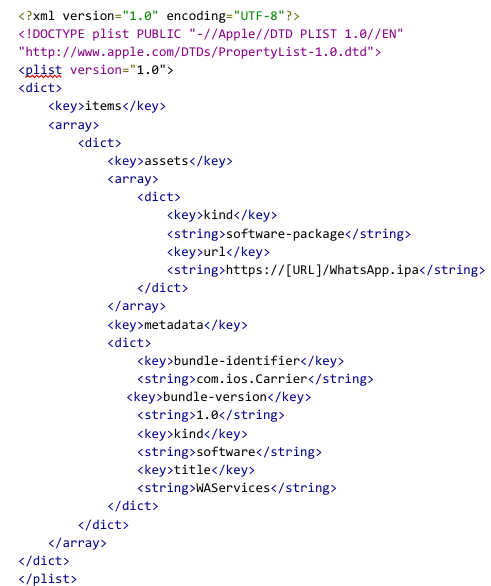
The resulting application is signed with a certificate from a company named 3-1 Mobile SRL (Developer ID: 58UP7GFWAA). The certificate satisfies all of the iOS code signing requirements on any iOS devices because the company was enrolled in the Apple Developer Enterprise Program.
These apps still run inside the iOS app sandbox and are subject to the exact same technical privacy and security enforcement mechanisms (e.g. code side loading) as any App Store apps. They can, however, be sideloaded on any device and don’t need to be installed via the App Store. We do not believe the apps were ever available on the App Store.
The app is broken up into multiple parts. It contains a generic privilege escalation exploit wrapper which is used by six different exploits. It also contains a minimalist agent capable of exfiltrating interesting files from the device, such as the Whatsapp database.”




